Another Alaska agency says it’s become the victim of a cybersecurity “incident,” making it the fourth to disclose such a disruption in the past year.
The Alaska Seafood Marketing Institute, which operates separate computer systems from the state’s executive branch, discovered the activity of a “nefarious third party” in August, said Jeremy Woodrow, the institute’s executive director.
It took weeks for the institute to fully recover from the incident, which Woodrow declined to characterize as an “attack.” But the effects were limited and only some employees and functions were disrupted, he added.
“It was just some lost time of business,” Woodrow said in a phone interview Monday. “It was a short-term blip that disrupted processes, but none that were not able to be corrected.”
ASMI is a public-private partnership housed by the state’s commerce department; it spends only federal grant money and tax revenue generated by the fishing industry.
As far as the institute is aware, Woodrow said, there was no impact from the attack on the Alaska public or the state’s fishing industry. Most of ASMI’s sensitive data, he added, is stored on separate state-run computer systems.
“The majority of the data we have is copyrighted photo and video files,” Woodrow said. “There’s not a lot you can do with that.”
Cybersecurity breaches have become a growing problem for Alaska agencies, and businesses and governments around the world, in the past year.
In December, state officials announced that hackers had compromised Alaska’s election systems and accessed the personal information of more than 100,000 voters.
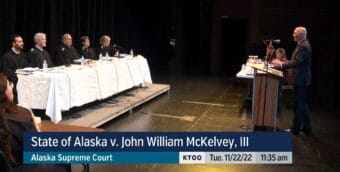
Then, in May, a disruptive attack hit Alaska’s court system, which also operates separate computer networks from Gov. Mike Dunleavy’s administration.
The same month, hackers forced the state health department’s systems offline, potentially exposing Alaskans’ protected health information. Months later, that agency and the Alaskans and health care providers it serves are still contending with the attack’s effects.
Both the court system and health department, along with state technology officials, have released few details about the nature of the attacks on those agencies, or about the identity of the attackers.
Woodrow, the seafood marketing institute, also declined to reveal many details about the incident.
Both the FBI and the state commerce department, he said, were involved in ASMI’s response. Spokespersons for the FBI and commerce department each declined to comment.
Woodrow said ASMI has also been working with Mandiant, a Silicon Valley cybersecurity firm that was hired after the attack on the health department earlier this year.
The company is drafting a report on the incident, though it will probably be kept confidential “because it talks about some of our inner workings,” Woodrow said.
He said ASMI is still waiting on a final version of the report, but he added that he thinks it can adequately protect its computer systems without asking for a bigger budget for cybersecurity.
“A lot of it’s the setup, and how you can do better within your own existing infrastructure,” Woodrow said.
Jack Schultheis, the chair of ASMI’s board, said he was “really pleased” with the way the incident was handled.
“It took a lot of time,” he said. “But everything turned out to be safe and secure.”