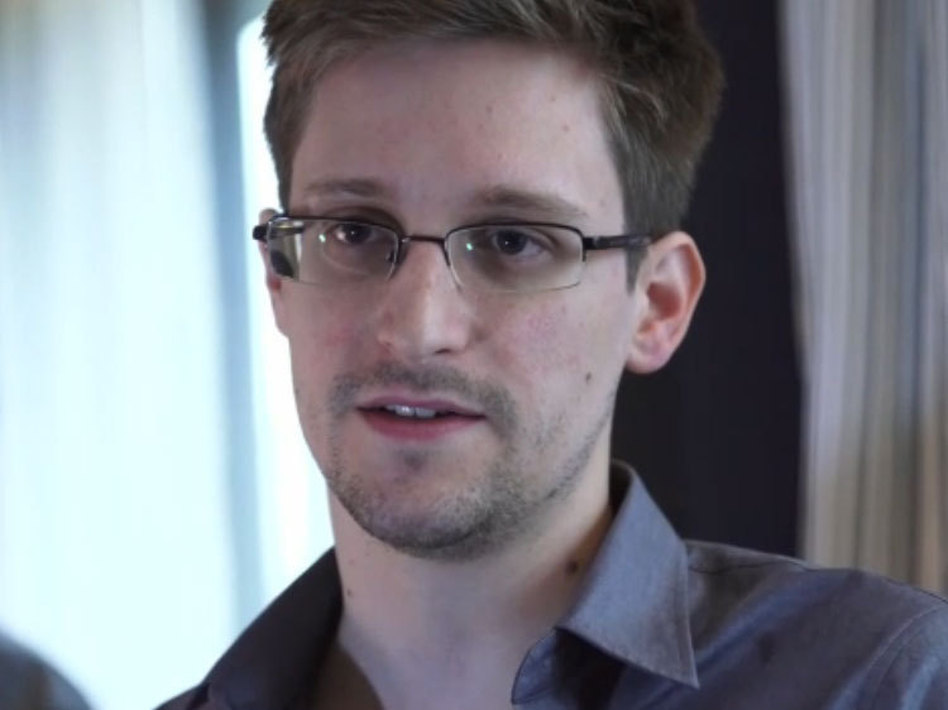
Basing its reporting on documents obtained by former National Security Agency contractor Edward Snowden, The Washington Post moved a story last night that details a close collaboration between the spy agency and the Central Intelligence Agency, when it conducts drone attacks against suspected terrorists.
As the Post reports this revelation may bolster the NSA’s assertion that its controversial practice of collecting vast Internet data is used for the purpose of protecting the country. The documents, however, do not make specific mention of any of the surveillance programs revealed by the Snowden leaks.
The Post story details the 2012 targeted killing of Hassan Ghul, a close associate of Osama bin Laden, who outlined the courier network that eventually led to his capture.
The paper reports that an intercepted email from Ghul’s wife gave enough detail that the CIA was able to order a drone strike against the suspected terrorist:
“In the search for targets, the NSA has draped a surveillance blanket over dozens of square miles of northwest Pakistan. In Ghul’s case, the agency deployed an arsenal of cyber-espionage tools, secretly seizing control of laptops, siphoning audio files and other messages, and tracking radio transmissions to determine where Ghul might “bed down.”
“The e-mail from Ghul’s wife ‘about her current living conditions’ contained enough detail to confirm the coordinates of that household, according to a document summarizing the mission. ‘This information enabled a capture/kill operation against an individual believed to be Hassan Ghul on October 1,’ it said.
“The file is part of a collection of records in the Snowden trove that make clear that the drone campaign — often depicted as the CIA’s exclusive domain — relies heavily on the NSA’s ability to vacuum up enormous quantities of e-mail, phone calls and other fragments of signals intelligence, or SIGINT.
“To handle the expanding workload, the NSA created a secret unit known as the Counter-Terrorism Mission Aligned Cell, or CT MAC, to concentrate the agency’s vast resources on hard-to-find terrorism targets. The unit spent a year tracking Ghul and his courier network, tunneling into an array of systems and devices, before he was killed. Without those penetrations, the document concluded, ‘this opportunity would not have been possible.'”
The whole piece is worth a read; it’s one of the most detailed looks at the controversial and mostly secret U.S. program of targeting and killing terror suspects.
9(MDEwMjQ0ODM1MDEzNDk4MTEzNjU3NTRhYg004))
Read original article – Published October 17, 2013 3:51 PM
